These threat actors have been then capable to steal AWS session tokens, the short term keys that enable you to request short-term credentials for your employer??s AWS account. By hijacking active tokens, the attackers were being ready to bypass MFA controls and attain usage of Safe and sound Wallet ??s AWS account. By timing their initiatives to c
 Jennifer Grey Then & Now!
Jennifer Grey Then & Now! Judge Reinhold Then & Now!
Judge Reinhold Then & Now! Keshia Knight Pulliam Then & Now!
Keshia Knight Pulliam Then & Now! Nadia Bjorlin Then & Now!
Nadia Bjorlin Then & Now!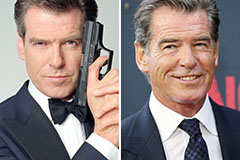 Pierce Brosnan Then & Now!
Pierce Brosnan Then & Now!